Why hire a vCISO?
EXPLORE THE DIFFERENCES BETWEEN CISO AND vCISO.
How REIFY helps your organization with cybersecurity.
Our focussed solutions are:
Customised
Cost-effective
Comprehensive
Services
Robust cybersecurity is not just an IT concern but a strategic business imperative. Reify offers Fractional or vCISO services for your organization with access to top-tier cybersecurity expertise and leadership, enabling you to fortify your defence, ensure compliance, and protect your critical assets without the overhead of a full-time Chief Information Security Officer.
Tailored to your specific risk profile and business objectives, we develop and implement comprehensive cybersecurity strategies that safeguard your operations, reputation, and bottom line.
Risk Assessment

Reify VCISO expert will start by identifying, analyzing, and prioritizing potential security threats to your IT systems, networks, and data. We proactively assess your cybersecurity vulnerabilities and determine how much damage a cyberattack could cause. Based on the risk assessment, we develop a plan to implement security controls that mitigate these risks.
These controls can involve technical measures like firewalls and encryption, as well as administrative procedures and staff security awareness training.
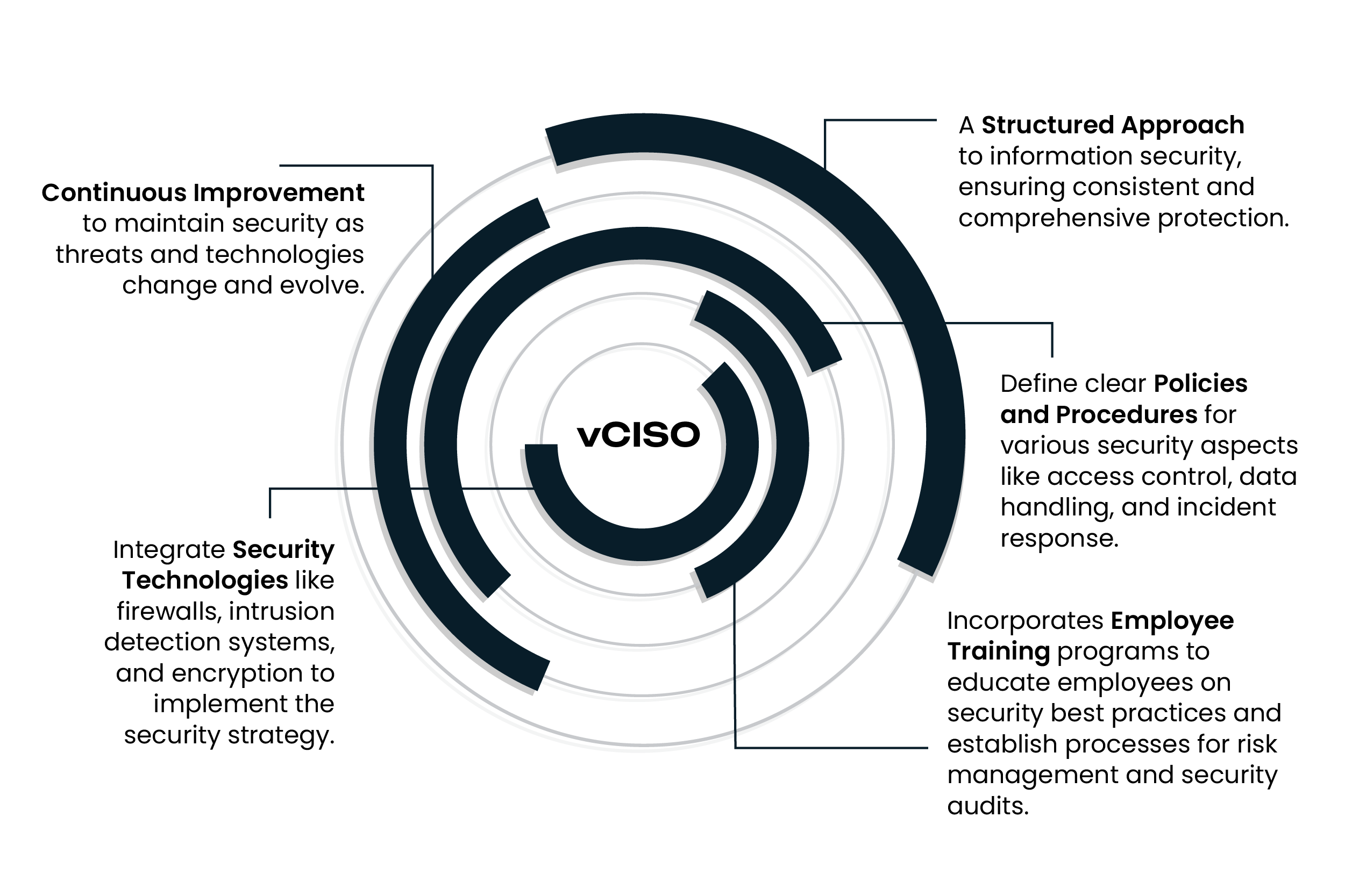
Comprehensive Information Security Program (ISP)
Based on the Risk Assessment, we prepare an Information Security Program customized to your organization’s needs. This is a crucial requirement to comply with government and industry security standards like PCI, HIPAA, HITRUST & SOC2.
An ISP is an overarching framework that manages and maintains your organization's information security posture. We will provide a collection of policies and procedures, recommendations for systems and tools designed to safeguard sensitive data and IT systems. This includes:

Data Breach: The threat is real!

83%
Organizations globally that have suffered more than one data breach.
$4.35 Million
Average cost of a data breach.
277 Days
Average number of days it takes to identify and contain a data breach
Source :
https://www.wired.com/